Starting today, the open tracking pixel we insert into your emails to track opens will look different. They will now be non-parameterized, encrypted URLs that are very, very difficult for pixel-blockers to detect.
Examples of pixel tracking in emails
Ever since email marketers invented a way to track whether someone opens an email, counter measures have been trying to block the ability to tell whether an email has been opened. Open tracking works by inserting an image tag into the email, where the image URL is unique to each recipient. If that particular image is downloaded by the email client, then the marketer knows that that particular recipient opened the email. It’s a trick email marketers and cold emailers have used ever since emails were allowed to contain HTML.
Typically a GMass tracking pixel looks like this:
<img height="0" width="0" src="http://ec2-52-26-194-35.us-west-2.compute.amazonaws.com/x/o?u=3D4836e6cc-0b4a-4d4b-8e75-39c04d139bf9&c=2724793">
Starting today, it will be non-parameterized and encrypted:
<img src="http://ec2-52-26-194-35.us-west-2.compute.amazonaws.com/OzqNT9U_4GWwWja0p6FyDFL3s1yl2LXMbKhKWmqIY3m2ZMlRqjIZtarzGOem8WXU6CiTUZUZLR6-f9QkENOu2cPbVfEdju_SSCo4x9Czk-rDQmi81_KcdchyrL6jFDCyhvcEop7GRYuvnD6DwSaFVwnEPNvGQVsPQp3hREWpqFuFZToXZWr">
If you look at other tracking pixels from popular email marketing services, they follow a similar format.
Tracking pixel from MailChimp:
<img src="https://thinkific.us20.list-manage.com/track/open.php?u=9ce134924e20d07b0555e3ef3&id=7bad33ad13&e=c6fc19945a" height="1" width="1">
MailChimp uses a standard pixel, with specified 1×1 dimensions and an image URL with three query parameters.
Tracking pixel from Constant Contact:
<img src="http://r20.rs6.net/on.jsp?ca=27edb7ff-a1da-440b-8e7c-e801ae93ae85&a=1123722063060&c=f76c377e-c2ba-11e9-8d07-d4ae52754007&ch=f76d3bec-c2ba-11e9-8d07-d4ae52754007" / alt="">
Constant Contact uses a standard pixel, without setting the height and width but with an image URL with several query parameters.
Tracking pixel from Twilio SendGrid:
<img src="https://u123847.ct.sendgrid.net/wf/open?upn=g0kn1nykOryF9fxxV-2BnyY4uXbKybbHq99YMco1LcmREUCWI6Peodkhk0W3kLkWZ9-2FRrgnOUd54RsBRa-2FNPrU081NM-2BK1BIHCBdb6CJNkvKemAAP3Rpjvz6ax5hdIc41G0isabMxwKW2YHfEjbqUW5Am6Uot2OsjUqBZ4DRBPEEKB6EJ74LiENRINjUi0vFHemTrDvS-2BAJmAKpYuOm2XiZOgbPhfMv-2FUrKZjAVDIMoT4-3D" alt="" width="1" height="1" border="0" style="height:1px !important;width:1px !important;border-width:0 !important;margin-top:0 !important;margin-bottom:0 !important;margin-right:0 !important;margin-left:0 !important;padding-top:0 !important;padding-bottom:0 !important;padding-right:0 !important;padding-left:0 !important;"/>
Twilio SendGrid gets the award for the longest tracking pixel URL and the most inline CSS, but they are a tad smarter than the rest, by encrypting the main parameter in the image URL. Still though, they are setting a height and width and using a query string parameter.
Tracking pixel from Customer.io:
<img src="http://email.domain.com/e/o/eyJlbWFpbF9pZCI6IlJOMjRCUU1BQVhNMFM5UjdzLXI3c1Z2RUdsVW1WQT09In0" style="height: 1px !important; max-height: 1px !important; max-width: 1px !important; width: 1px !important"/>
Customer.io is the smartest of the bunch, using a non-parameterized image URL and without setting the traditional height/width attributes in the image tag. This is very similar to what GMass is now doing, except for one key difference. The length of the Customer.io image URL will always be the same, and this makes it easy for a pixel blocker to identify it.
How pixel blockers work
Given the above examples of the image tag that tracks opens, you might be able to determine how a pixel blocker works. There are several attributes of an open tracking pixel that separate it from a “normal” image in an email, and if a pixel blocker can identify those attributes, it’s easy to block just the tracking images. Of course, a pixel blocker has to be careful to block only the tracking image and not the other images, because if the other images are blocked, and this upsets the user, the user will want to uninstall the pixel blocker.
What are those common attributes?
- Dimensions of 1×1 or 0x0
- An <img> src value with query parameters
- A discernible length for all tracking pixel URLs
A smart pixel blocker can identify all 1×1 or 0x0 pixels from the img “src” attributes and block them, figuring that even if they are part of the email design and not a tracking pixel, the effect on the rendering of the HTML email is likely minimal since a 1×1 pixel is so small, or in the case of a 0x0 pixel, invisible. Blocking all 1×1 pixels is more dangerous because there might also be a legitimate 1×1 pixel that’s part of the design of the HTML email.
Additionally, if the image URL has query parameters, that’s a dead giveaway that it’s likely a tracking pixel. It is exceedingly rare for an image that’s actually part of the email design, and not a tracking pixel, to contain query string parameters.
Lastly, whereas the image URL of “normal” images in an HTML email will vary in length (for example, logo.png is a different length than header-banner.jpg), if an email service provider’s image tracking URL is consistently the same length and always contains the same number of query string parameters, that makes it easily identifiable by a regular expression parser looking to block tracking pixels.
What are some common pixel blocking tools?
Back when I first launched GMass on Product Hunt, there was another product that launched around the same time called Ugly Email that was #1 for the day. It was a Chrome extension that blocked open tracking pixels. It was popular for a while, but it looks like the product has ceased development, as the last update on the Chrome store for Ugly Email is from July 2018.
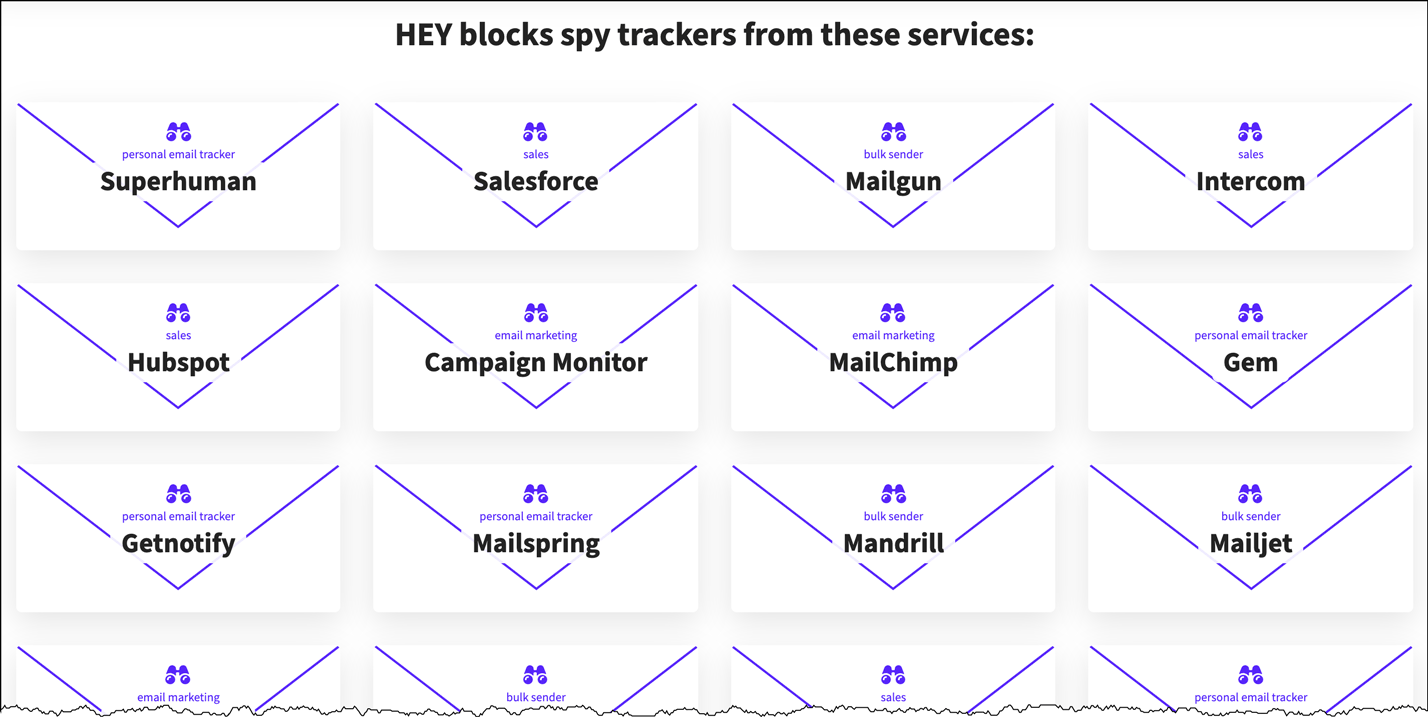
Other more current pixel blockers include Chrome extensions like PixelBlock and Email Privacy Protector and most recently, a new consumer email service called HEY claims to block the tracking pixels of many email service providers, and they go so far as to publish a list of all the tracking pixels they block.
Note that GMass isn’t on the list, likely because we haven’t come across their radar yet. I suspect that we eventually will, and this makes our new open tracking technology even more relevant.
HEY’s competitor is Superhuman, a fancy email client that’s popular among Silicon Valley types. Superhuman landed in hot water because it inserted a tracking pixel in all sent emails by default unless a user turned the feature off. To quell the uprising, they reversed course and had the feature turned OFF by default but still let users turn it on. Additionally, Superhuman blocks tracking pixels in received email by default, via this setting:

But I’ve tested our new encrypted open tracking mechanism, and it does indeed get past Superhuman’s blocker. Here’s a notification from my own Opens folder in Gmail:

Notice the User Agent…Superhuman!
How we’re getting around the pixel blockers
If you study our new format for the open tracking pixel, you’ll notice that it:
Does not set the height and width attributes
This makes it impossible to tell the size of the image before it’s downloaded. And once it’s downloaded, it will register as an open. So blockers can’t use its size to determine whether to block it from the user. The exception would be if a blocker had the infrastructure to download all images in all emails to “fool” the email tracking system, and then only present the non-1×1 and non-0x0 pixels to the email client, but I’ve never heard of this happening.
Does not have query parameters
We have removed the question mark (?) and the query parameters from our image URLs so that they look like “normal” images.
Has a varying length
Every time you send an email campaign with GMass, the open tracking URL will have a different length. That’s because we’re using an AES encryption algorithm that encrypts the parameters into a variable-length string.
Allowing the customer to set a tracking domain
You might notice that the host of the pixel is http://ec2-52-26-194-35.us-west-2.compute.amazonaws.com, which is our AWS server that handles tracking. A pixel blocker could identify this string and block it, but then a lot of other elements of an email would also be blocked. Still, it’s best to set a custom tracking domain like email.yourdomain.com to brand the image URLs and avoid this problem altogether.
I hope that you’ll find this innovative way of handling open tracking a reason to choose GMass over other email sending tools because nobody else has thought this problem through like we have.
More Reading
If you’re interested in learning more about email tracking, I recommend reading these articles:
- This Wired story about how email tracking became so popular
- The Wikipedia article on email tracking.
- The blog post that caused controversy for Superhuman.
Update – July 19, 2020
The company behind HEY discovered this blog post and has now implemented a method to block our new encrypted tracking pixel. Many people have been asking me what my next move is. For now, we’re laying low. We could alter our algorithms to circumvent their blocking again, but I don’t see the point of escalating the matter. The amount of email we we deliver to hey.com is minimal, and if it starts to climb, we’ll re-examine the issue.
Only GMass packs every email app into one tool — and brings it all into Gmail for you. Better emails. Tons of power. Easy to use.
TRY GMASS FOR FREE
Download Chrome extension - 30 second install!
No credit card required


Absolutely Amazing Ajay! This is something that I was starting to become concerned about, particularly with the constantly evolving counter-measures out there. I figured you and your team had it handled! This is what I pay for as an incredibly satisfied GMass,co customer!
Thanks Zach. I never know how much interest there is in the technical underpinnings of GMass, but your comment validates our efforts!
Great work buddy! – Rick (GuessBox et all)
Dear Ajay,
I would like to know about the contact limit to which I can send emails through Gmass Premium per day and also per month.
Also, Want to know about all features, plz help in knowing the same.
Thanks.
“but I’ve never heard of this happening.”
Well it’s happening, this is not as smart as you’re making it sound like, caching is obviously been used for years now.
You’re right, and Gmail has been using an image proxy for years now. Still though, Gmail has to download the image first, and that is what registers the open.
Why do my emails get blocked?
I’m not sure.
Why don’t you randomize the size in the tracking pixel 2-10 for random height and width and since it’s loading a clear/transparent gif it won’t matter.
That is a potential counter measure for the future! Randomizing to a 10×10 pixel though could throw off the design of the email.
But can we still define it to be transparent and with no padding, so it wouldn’t effect the other elements of email for its design?
What would prevent a provider from just downloading the images when the user receives the email and then serving the downloaded copies from cache?
A provider can certainly do that, but when the provider FIRST downloads the image, that is what will register as the open. We haven’t seen a system that downloads ALL images of ALL emails into its cache, regardless of whether the user opens that email — if a system did that, then it would register an open for all emails even if they haven’t been opened.
This is great. Look forward to seeing it in action!
Thanks Mohit.
Services like Hey are also using image caching and proxy services as way to get around this. I think Hey calls it a VPN for Images and assets.
How does this approach handle a scenario where after the first load, subsequent opens aren’t trackable as the image is served from the cache and not from the origin server each time?
Granted you can track the initial delivery and open, but you won’t be able to log the subsequent opens right?
That’s correct. HEY is doing this, and Gmail has done this for years. Despite HEY claiming to provide a better alternative to Gmail, they sure did copy a lot of its features.
You are correct that the initial open will be registered, and subsequent opens are likely determined by the length of time in between the opens. The cached image likely doesn’t last forever, although I haven’t tested HEY enough to know exactly how long it lasts. With Gmail though, it’s possible to register multiple opens in a short period of time.
Let’s be honest, hardly anyone is going to be using HEY compared to other platforms. If you’re on Google’s Gsuite, for example, it’s a huge deal to move your email to another provider and you would lose all the benefits of an integrated tool suite. If Google start losing customers they will just make a few tweaks. Simply can’t see HEY taking off despite a lot of self-promotion from the creators.
Hi Ajay,
Awesome job.
So, as I read your email announcement, it’s working from today – no actions needed from user end to get it working?
Be well everybody
Max
That’s correct…it just works!
Has anyone thought that maybe pixel tracking is a privacy concern? Why are you so proud of what is essentially setting up a camera up peer into your neighbors window to know if they opened and envelope you sent to them?
Because then users know whether they should send more envelopes to them.
Exactly. What a nightmarish thing to be proud of.
Truly insane to be proud of something so obviously shitty. Do something more important with your life.
I feel pretty good about the value I bring to hundreds of thousands of people that rely on email to communicate with their audience.
Stop using doublespeak and euphemisms to avoid confronting your despicable behaviour.
The “value” in this case, to the thousands of people who rely on email to “communicate” with their “audience” is EXPLICITLY a means for them to ignore their audience’s specific preference to not be tracked.
From your own post:
> Additionally, Superhuman blocks tracking pixels in received email by default, via this setting. But I’ve tested our new encrypted open tracking mechanism, and it does indeed get past Superhuman’s blocker.
The logic you use to defend yourself is about as edifying on an intellectual level as an arms dealer claiming that they only *export* munitions to genocidal regimes. Hey, I feel great about the value I’m providing to them! And *I’m* not the one killing people, right?
(Of course even an arms dealer could argue that their weapons can be used to keep the peace. What you have enabled above is explicitly a means for circumventing a user choice to not be tracked.)
>>Stop using doublespeak and euphemisms to avoid confronting your despicable behaviour.
Please provide examples of doublespeak and euphemisms. I don’t see any.
>>The logic you use to defend yourself is about as edifying on an intellectual level as an arms dealer claiming that they only *export* munitions to genocidal regimes. Hey, I feel great about the value I’m providing to them! And *I’m* not the one killing people, right?
Your comparison is half correct. I do feel great about the value I’m providing my customers. I am not, however, killing anyone or enabling any killers.
> Please provide examples of doublespeak and euphemisms. I don’t see any.
Here’s a glossary for you! (I did put these in speech marks for you but apparently that wasn’t clear enough :))
“Value” — the value you’re talking about here is a means to bypass privacy preferences set by a user.
“Communicate” – spam
“Audience” – people who have specifically opted out of being tracked by your customers
“I feel pretty good about the value I provide to hundreds of thousands of people who use bullets to communicate authority with their audience”
> Your comparison is half correct
It’s not a comparison, it’s an analogy.
> I am not, however, killing anyone
Nobody suggested you are. Oh dear.
Don’t know why you feel so proud of allowing companies to spy their customers.
I’m proud of the intellectual prowess that solving this problem required. As for open tracking in general, that’s an email marketing industry standard. And if you more broadly apply the definition of “spy”, everyone who sees you walk through Times Square is spying on you.
> intellectual prowess
Yes, hearty congratulations on copying customer.io’s solution and varying the length of the image locator. I’ve taken the liberty of notifying the Royal Swedish Academy so they can introduce a new category for the Nobel prize committee.
> solving this problem
Can you explicitly state what the problem is you solved? I just want to hear you say it.
Not many people would think that “Users can opt to prevent my scumbag service from secretly monitoring every time they open an email” is a problem. They’d think that’s a fundamental right.
> an email marketing industry standard
Yes, in the same way as civilian casualties are a standard for cluster munitions. Your complicity is not mitigated by the fact that many companies are also unethical, and you are literally boasting in this blog post that your “solution” (again: nobody would consider the thing you “solved” a problem except creeps who want to spy on their users) is novel. You’re literally losing track of your own argument for god’s sake.
> And if you more broadly apply the definition of “spy”
It’s good of you to explicitly signpost the fact that you’re about to introduce a logical fallacy into your argument.
> everyone who sees you walk through Times Square is spying on you.
I guess there’s not much to be gained from speaking to someone stupid enough to think that this point furthers their argument in any substantive way, but maybe if I use small enough words we’ll make some progress.
1. There is no reasonable expectation to privacy in Times Square, or in public in general with a very few exceptions,
2. A private citizen or organisation could “spy” on you in Times Square: they could log where you go, how long you spend there, your clothes, etc. But nobody, anywhere, with a couple of brain cells to rub together, could reasonably consider that people “seeing” other people in Times Square is surveillance or spying, because it’s tacit observation, not an active decision to surveil,
3. If a citizen or organisation did decide to spy on someone in a public space, and was exposed doing it, they’d rightly be pilloried for their creepy behaviour. The “it’s not illegal” defence would be dismissed by anyone with an ounce of integrity who recognises that the basis for a behaviour being just is not whether or not it is precluded by the law, but by what is decent,
4. If the citizen being surveilled specifically asked the organisation or individual surveilling them to stop doing it, and the counterparty continued, then the citizen would have legitimate grounds to seek an injunction preventing the counterparty from doing so.
5. There is, of course, a reasonable expectation of privacy in an email inbox wherein I have explicitly specified that I would like tracking pixels, and other covert means of monitoring my behaviour, from being blocked.
This honestly might be the stupidest vitiation of one’s own argument I’ve ever seen on the internet, and that really is saying something.
>>Yes, hearty congratulations on copying customer.io’s solution and varying the length of the image locator. I’ve taken the liberty of notifying the Royal Swedish Academy so they can introduce a new category for the Nobel prize committee.
Actually, I came up with my idea on my own, and then I researched how other providers were doing it, during which I happened upon Customer.io’s solution. Still though, varying the length is a significant and non-trivial improvement. I’ll look forward to hearing from the RSA.
>>Can you explicitly state what the problem is you solved? I just want to hear you say it.
Umm…did you not read the blog post? It’s pretty clear what the problem I solved is. I’ve made open tracking more accurate.
>>Not many people would think that “Users can opt to prevent my scumbag service from secretly monitoring every time they open an email” is a problem. They’d think that’s a fundamental right.
No idea what you’re talking about here because your quote is neither the perspective of me, my customers, or the recipients of email.
>>Yes, in the same way as civilian casualties are a standard for cluster munitions.
1. Except that I’m not killing anybody.
2. The problem I’m solving is for my own users.
>>It’s good of you to explicitly signpost the fact that you’re about to introduce a logical fallacy into your argument.
I was offering a corollary based on the HEY team’s definition of a spy in this blog post: https://m.signalvnoise.com/mailing-list-software-should-stop-spying-on-subscribers/ which is “a person who secretly collects and reports information on the activities, movements, and plans”
You remind me of myself in my 20s. I too used to string together big words in hopes of sounding intelligent and logical. I’ve evolved though and can now do both simultaneously (6 syllable word).
> Umm…did you not read the blog post? It’s pretty clear what the problem I solved is. I’ve made open tracking more accurate.
It’s hilarious watching you try to squirm out of this. Yes, I read your self-aggrandising blog post. The question was a rhetorical device, but as you’ve previously demonstrated a limited ability for abstract thought, here is an explicit question for you with a yes or no answer:
Have you or have you not created a workaround for your customers to silently override the privacy settings of apps like Superhuman and HEY by tracking users who do not believe that they are being tracked?
Spare us all the bullshit about value creation, audiences, and the accuracy of open tracking. You know what you’ve done, it’s just funny that someone as patently devoid of anything beyond self-interest is unwilling to acknowledge it. You’re selfish. It’s OK, you can admit it. We’ll all respect you more for it.
> No idea what you’re talking about here because your quote is neither the perspective of me, my customers, or the recipients of email.
It’s not a perspective, it’s a fact. You have created a means of silently overriding the settings of privacy-focused email apps. Your blog post is titled “How we get around tracking pixel blockers”.
I am a person who receives marketing emails and uses HEY. I am therefore disproof by counterexample of your final claim.
“No idea what you’re talking about” makes you look like you have dementia in the context of this discussion. You are repeatedly evading the point which is being flagged to you time and again by people in this comment section: you have created a means for email marketers to silently track users without their consent, when they have explicitly opted out of tracking.
> Except that I’m not killing anybody
Capacity for abstract thought: 0/10
> The problem I’m solving is for my own users
Wow, finally something approaching an acknowledgement of how myopic you are. Do you acknowledge that in “solving” a “problem” for your users, you’re enabling them (actually is there even a way for a Gmass user to opt out of this if they *wanted* to respect the privacy of customers who specify that they’d like to not be tracked? If not, you’re not enabling it, you’re forcing even your privacy-conscious users to be as unethical as you) to track customers who do not want to be tracked? Yes or no?
> I was offering a corollary based on the HEY team’s definition of a spy
It falls down immediately because their definition of spy is regarding the collection of information. Nobody who sees me walking through Times Square is collecting any information about me.
[Big gap where you ignore myriad points which prove your logic to be stupid beyond belief.]
> You remind me of myself in my 20s. I too used to string together big words in hopes of sounding intelligent and logical. I’ve evolved though and can now do both simultaneously (6 syllable word).
We have nothing in common for two reasons. Firstly I don’t consider any of the words I used to be big words, and secondly I engage with the substance of what people say. Everything about your replies screams of a man dissatisfied with the fact that part of his vocation is enabling the erosion of privacy, on behalf of an industry almost universally hated by folks everywhere. You claim people receiving the emails don’t mind, but you silently exfiltrate their data instead of making it opt-in. You claim you love your work but you have repeatedly pretended to be ignorant to the fact that you’re enabling your customers to ignore the privacy settings of their customers.
I know you probably thought of this blog as a safe space for your crony customers to jerk themselves dry over the latest mail merge feature in your little Chrome extension, but do us all a favour and call a spade a spade: if it wasn’t for folks like HEY, you’d have run roughshod over my desire to not have dimwitted spammers tracking when I open my emails.
You initially seemed to at least be brazen enough to own up to it, but you’re terrified of going anywhere near the fact that you’re overriding my privacy settings.
“email marketers and cold emailers”?
You mean spammers?
Spammers are evil. If you help them, *you* are evil.
I’m not saying that I help spammers, but if you place a label like “evil” on an entire person for one aspect of their lives, you are naive. See what I did there?
I suppose I could have said, “I fear you have not given proper respect to the privacy concerns of people who use the internet, and find it a little creepy when unwanted advertisements chase them from one web site to the next; nor have you given proper consideration to the ethical implications of doing business with ‘cold emailers’, who are more commonly known as ‘spammers’ and are one of the most reviled & unwelcome groups of people on the internet.”
But a riff on the (long-abandoned) Google promise, “Don’t be evil,” seemed a little punchier.
If you can make money doing an evil thing, does that make it less evil? If I choose not to do an evil thing, am I naive to forego all the money I could have made by doing it? Is profitability the only ethical standard that matters?
P.S. Sensibly-written mail clients don’t load *any* remote content without explicit, per-message permission from the user. Most of your “innovative” tracking pixels stay on the server anyway.
On your quote:
It’s not my job or mission to give respect to the privacy concerns of the minority of Internet users who feel violated by email open tracking. So now you’re against retargeting ads too? Better take that up with Facebook and Google. If cold emailers were so reviled and unwelcome, they wouldn’t be closing deals left and right as a result of their cold emails.
On sensibly-written mail clients:
Explicit, per-message permission? Then there are no sensibly-written mail clients. Even HEY loads remote images without asking per-message permission.
Ruh-roh! You’re losing track of your own arguments again!
First your dumb-as-a-brick argument was that folks receiving these emails don’t share the “perspective” that this is a privacy concern. (I guess those folks aren’t the people coming into the comment section here to berate you, huh?)
Now you’re saying that whilst it IS a privacy concern, it’s not your problem because it’s not your “mission” to “respect” their concerns.
And apparently cold emails are “closing deals left and right”, but you still need to build workarounds for the “minority of internet users” who block tracking? Got it. Makes total sense.
This is the closest you’ve come to the truth: your job and “mission” are actually totally at odds with privacy concerns for users. Taking the decisions you have reduces their ability to be private. And, of course, you’re aware of this and content to behave like a scumbag, or you’d be giving users a choice in whether your service tracks them.
> So now you’re against retargeting ads too?
Are you a Trump supporter by any chance? Because this sort of inane whatabouttery is the sort of bullshit they use to defend the indefensible. “I’m not saying what I do is bad, but if you think it is, look at all these other bad things other people are doing! Are you going to criticise them too?”
Drop it. People are here, right now, giving you the gift of feedback. Ignore for a second the fact that Safari and other browsers block third-party cookies by default, and that Chrome will too in the next 18 months. But it doesn’t matter: you don’t work at Google or Facebook. You don’t have control over their products. But yeah, I hate retargeting too.
> If cold emailers were so reviled and unwelcome, they wouldn’t be closing deals left and right as a result of their cold emails.
{Citation Needed}
The marketers in this thread seem to have a delusional perspective on how effective their emails are. Anyone would think that cold emailing is so effective that, I dunno, you don’t need bullshit invasive features for the “minority of internet users” you’re screwing with this scumbag behaviour.
> Explicit, per-message permission? Then there are no sensibly-written mail clients.
Airmail lets me disable images and enable them on a per message basis. I suspect HEY will soon. The bell is tolling for scumbag marketers!
Not everyone who email markets is spamming.
When you buy your favorite music from Apple, Amazon, or Google and then they let you know or a new release from that artist’s catalog, that’s not spamming any more than a high end restaurant suggesting a wine pairing for the meal you ordered.
You have established an interest and the retailer, artist, or sommelier is giving you further info based on that interest.
Netflix and Hulu do that too with customized screens based on what you watch.
If you find that evil, you live in a very weird world view where any help or suggestions to get you more of what you like are evil.
If I have an account with an online store or service, if I’ve previously bought something from them, they don’t need tracking pixels in email to know my interests & suggest further purchases. They don’t need email at all, they can do all that in the store.
Only spammers – excuse me, ‘cold emailers’ – need to spy on people.
Except of course that this blog post is about a feature which, caps incoming because you seem to have missed it, EXPLICITLY OVERRIDES A USER’S PREFERENCE TO NOT BE TRACKED.
If Apple, Amazon, Netflix, or anyone sent me notifications about something I had asked them not to, then of course it would be spam.
This comments section is full of scumbag marketers rejoicing that they can track customers who don’t want to be tracked and consumers asking why their preferences are not being respected. Not seeing many consumers celebrating their preferences being ignored, but maybe they’ll be here in a minute.
>>Except of course that this blog post is about a feature which, caps incoming because you seem to have missed it, EXPLICITLY OVERRIDES A USER’S PREFERENCE TO NOT BE TRACKED.
That’s correct. I’m prioritizing MY USERS’ desire to have accurate open tracking over the minority of email users who don’t want to be tracked. Since those general public email users aren’t my users and since what I’m enabling my users to do isn’t harming those users, I don’t have an ethical issue with what I’m doing.
Getting closer to the truth! Just go ahead and say it: you want money more than you want to respect people’s privacy. Admit it dude.
No ethical issue, hahaha, spying on people without consent, explicitly ignoring their wishes, getting smug about being shady. You are heading in the opposite direction of being a good person. Most people don’t want to be tracked.
Ajay said “isnt harming those users” is a sociopathic conclusion. If aperson does not want a thing to be happening to them and you enable the person doing it to continue to do it you are an accesory to the abuse.
I would admire you more if you owned the sociopathy and stated that you simply DONT CARE if a person does not wan to be tracked. That at least would be honest.
You are the cowardly side kick of the playground bully, holding his coat and yelling Go on, hit him again…… so sad
spam versus marketing is not really the issue surely? I a person does not want it known that they have or have not opened an email, and have gone to the lengths of installing software to prevent it, and that has been circumvented by the person wishing to know if it was opened……
THAT is the moral question. Not is it clever or its fine if its not spam. It is a matter of who has the right to knpow what a person is doing, the person or someone seeking to communicate with tem.
In the end it will be legislated against if enough people are concerned enough. Otherwise it will continue.
If legislated against the Ajays of the world will move on to teh next thing that is still not illegal, irrespective of the morality.
This was a great read and keeps my trust that GMass will continue innovating in the years to come.
Thanks Rahul!
Honestly glad that HEY has already blocked you. To think that you believe that this is valuable and an innovation shows how misplaced your principles are and what a waste of your time that could have been spent on something that helps humanity.
As the saying goes: I hope that your reap what you sow. If that’s for good … even better. If not, then I hope that you get tracked to death. Your choice.
I feel pretty good about my values, and my company is a reflection of my personal values. Feel free to track me all the way to my house. Although you’ll have to deal with this: https://www.dropbox.com/s/m6u8mpqgjvq76ps/Screenshot%202020-07-18%2002.59.32.png?dl=0
> my company is a reflection of my personal values
And what values would those be? The right to have your request for privacy ignored by spammers?
This is a ridiculously unprofessional comment, and reflects poorly on your company.
Also, “You may not use GMass to send spam. Spam, by definition, is unsolicited email sent in bulk.” That’s from your own Terms of Use. Yet the service you provide exactly fits that definition. Bulk unsolicited email. That’s approaching politician-level hypocrisy.
That’s really nice Ajay Ji. We can track better now.
We are becoming addicted for GMass in the recent COVID times for sending invitation for webinars. Incorporating the feedback in sheets was great.
Still, handling HTML templates in Gmail is the biggest pain in sending invitations.
Thanks.
Raghav
Wow Ajay, you are a cool programmer.
It seems like the smart approach of those that would block you and other trackers is to have the server ‘open’ the email immediately, dozens of times. False positives would make the information worthless.
Do you think that’s likely? It’s certainly technically easier and ends the cat and mouse game.
Interesting and noted! Thanks for the thoughtfulness of this.
Hi Ajay. This is interesting. I was wondering how you ensure that your customers are able to obtain opt-in consent required under e-Privacy Directive & GDPR if they’re Controllers in the EU and/or processing the personal data of subjects in the Union? How does that work in practice?
You’re disgusting. People like you who have no respect for privacy are exactly why I will never allow my email provider to display HTML emails.
If you believe that people want to be tracked as they open their emails, why do you need to dedicate so much energy towards clandestine tracking techniques? Surely you could just load an HTML link into each email which either opts the user into tracking in perpetuity when clicked (“Click here so we can track when you open emails from us”), or allows tracking on an email-by-email basis, requiring a click each time?
Far more than the immorality of exfiltrating sensitive information about users who are totally unaware of what you’re doing (and boasting of the “intellectual prowess” of… copying someone else’s solution and randomising the length of the image URI, only for HEY to make some changes which leave your solution DOA just two days later), I find the intellectual dishonesty on display here to be hilarious. You seem to believe that “tracking pixels” (euphemistic in the extreme: “monitoring pixels” would be better) serve some sort of consumer benefit, but everything about the manner in which you enable them suggests that you know that consumers, if given an explicit choice, would opt-out in droves.
Users of privacy-conscious email services like HEY are explicitly opting out of being tracked by spammers and spam-enablers like you. Why are you going to great lengths to ignore their choice? You are boasting of the fact that Superhuman users can opt-out of email tracking, but that emails sent with your service will still be tracked. Why do you think that’s acceptable? In a nested comment above you liken it to a direct mail marketer wanting to know whether or not they should send more envelopes of junk mail to a person’s postal address. But behaviour like yours, and the fact that at no point the twenty or so years I’ve had an email address has any email marketer ever stopped sending me emails because I didn’t open their emails, is precisely the reason that services like HEY have begun to appear: your industry has demonstrated repeatedly that it is unable or unwilling to behave with any integrity whatsoever.
The comment section of this blog post is filled with two kinds of comments. There are email marketers thanking you for building this, and there are consumers attacking your behaviour. Conspicuous by their absence are consumers thanking you for overriding the privacy options of their email clients.
You seem like a reasonably bright guy (aside from taking pride in removing size parameters and randomising the length of a resource filename), so have a think about the fact that most people would rather your entire industry did not exist. Only 11% of UK consumers “enjoy adverts”[1], 55% object to being targeted by adverts, and a similar number are “completely apathetic” towards advertising[2]. It seems probable that if you gave the average UK consumer the ability to click their fingers and magic away the entire industry, they’d do it.
You are dedicating your life to something people hate. I don’t pretend to know anything about the choices or pressure which led you to this point, but my advice is that if you intend to keep building things which enable a behaviour people hate, you might want to wind your neck in and stop boasting about building features which literally prevent consumers from exercising their right to not have you and your customers snooping on their emails, or do the honest thing and admit that you care more about money than you do about humanity.
[1] https://www.warc.com/newsandopinion/news/just-11-of-uk-consumers-enjoy-advertising/41945
[2] Ibid.
George, if people didn’t keep buying things from emails, marketers would stop sending them.
But, while most people say they don’t like marketing emails, they basically all click on them or buy things from them.
We send emails to our customers with new products, offers, etc, and they buy things from them.
Oh dear. Rob, this is a brilliant insight into how halfwitted most marketers are.
1. Anyone who has read my comment and goes on to read your reply will realise that you’re not addressing any of the points I make. Your reply is a total non-sequitur. You may as well be trying to refute my argument with a photo of a chimpanzee smoking a cigar.
2. Consumer sentiment towards marketing emails has little to do with their efficacy, although the maths you imply is, um, wrong.
3. A quick straw poll of open rates and click through rates suggests that you’re either the world’s greatest email marketer, a simpleton or a liar. (No prizes for guessing which it is!) Open rates of 15%-25% suggest that 75% of most “audiences” ignore each email, and CTRs <10% equate to 90% of even those who read the email not being interested in the content (I'd suggest that a good portion of those are opening it to delete it.)
3. To help you out with the maths, since you apparently think that <10% is the same as "basically all people", if you send an email to 10,000 people, with a 25% open rate, a 5% CTR, and a 10% conversion to paid, you have emailed 10k people, seen 7,500 ignore your email, 500 click through, and 50 convert to paying. That's 99.5% of people not converting to paid.
4. The problem that the bozos who find themselves running email marketing campaigns have is that they see engagement as validation but see a lack of engagement as passivity, when it's not. Consumer sentiment suggests that people hate the dreck you send out, and open and click through rates back this up.
>>If you believe that people want to be tracked as they open their emails, why do you need to dedicate so much energy towards clandestine tracking techniques?
I don’t believe that people WANT to be tracked. But I do believe that most people don’t MIND a company that has sent them an email knowing that they’ve opened that email. And for the few that do mind, yes, I’m prioritizing my users’ wishes over theirs.
>>You seem to believe that “tracking pixels” (euphemistic in the extreme: “monitoring pixels” would be better) serve some sort of consumer benefit, but everything about the manner in which you enable them suggests that you know that consumers, if given an explicit choice, would opt-out in droves.
Oh? Even Mike Industries, the godfather of the anti-Superhuman movement, disagrees with you on the consumer benefit angle: https://mikeindustries.com/blog/archive/2019/07/superhuman-is-spying-on-you#more-29080:~:text=Mass%20mailing%20companies%2C%20for%20the%20most,who%20haven%E2%80%99t%20opened%20them%20in%20months.
>>Users of privacy-conscious email services like HEY are explicitly opting out of being tracked by spammers and spam-enablers like you.
Not every HEY user is anti-tracking: https://medium.com/@JamesCridland/hey-com-email-first-impressions-bb51e56f6f18#3e2e:~:text=Anti%2Dtracking%20is%20good%20and%20bad
>>The comment section of this blog post is filled with two kinds of comments. There are email marketers thanking you for building this, and there are consumers attacking your behaviour. Conspicuous by their absence are consumers thanking you for overriding the privacy options of their email clients.
Well that would be like me thanking the IRS for allowing me to pay my taxes.
>>Only 11% of UK consumers “enjoy adverts”[1], 55% object to being targeted by adverts, and a similar number are “completely apathetic” towards advertising[2]. It seems probable that if you gave the average UK consumer the ability to click their fingers and magic away the entire industry, they’d do it.
You hit the nail on the head here. If they could click their fingers and magic away it, they would do it. BUT, if they had to put 5 minutes of effort into not being tracked, they would not. Why? Because it’s likely just not that important to them. I tell myself every day that I want to lose 20 pounds. If I could click my fingers and have that happen, that would be great. But I have to put some effort into losing those 20 pounds. So then, how much do I really care about losing those 20 pounds? Probably not that much.
>> I don’t pretend to know anything about the choices or pressure which led you to this point…
The choices or pressure? You make me sound like I’m a drug mule risking my life traveling across the border for a cartel in hopes of escaping poverty. I live a decent life, and I’m happy with most of the choices I’ve made so far.
>>but my advice…
https://medium.com/psychobabbling/the-psychological-reasons-you-shouldnt-give-advice-to-anyone-3529936330c4#:~:text=Giving%20advice%20is%20a%20selfish,help%20them%20with%20their%20thoughts.
>>do the honest thing and admit that you care more about money than you do about humanity
Wow. If I were a teenager, I would hashtag my response to this comment with #wowjustwow. I care about money. I care about humanity. Which do I care about more? Well, if I could make all the money in the world, but all of humanity were suffering around me, I couldn’t have a lot of fun with my money, so that doesn’t work. So hmm, what if I could earn a decent living in my role as a software developer, improve the lives of my thousands of users, and not have anyone murdered by placing a tracking pixel in the emails they get? That sounds like I have money and humanity in good balance.
> I don’t believe that people WANT to be tracked.
For a person with an ounce of morality this would be the end of the conversation. People do not want to be tracked. You enable it.
> But I do believe that most people don’t MIND a company that has sent them an email knowing that they’ve opened that email.
And yet everything about your work speaks to the opposite. If people don’t mind it, why not tell them you do it? Why are you scared? If you mean the above, then why would you not add a message like this to all Gmass messages:
“Just to let you know, we track you every time you open this message and share that data with the person who sent it. We do this even if you specify that you don’t want us to track you or if your email client tries to stop us.”
People don’t mind, right?
I’m also sure that with your god-tier intellect for “solving” “problems” you could create a system to make this all opt-in, rather than something they can’t even opt out of because you make the decision that they should be tracked no matter what their preference is.
> And for the few that do mind, yes, I’m prioritizing my users’ wishes over theirs.
The simple fact is that most people don’t know that you do this. You know it and I know it. It’s not that a minority of people care, it’s that a minority of people know. People are going to cotton on to this and start calling you out for it. Because it’s scumbag behaviour to deliberately take action to ignore a user’s preference on privacy.
> Oh? Even Mike Industries, the godfather of the anti-Superhuman movement, disagrees with you on the consumer benefit angle:
Roaring with laughter at how moronic it is to use an essay which could literally be a word-for-word takedown of your awful behaviour to refute a subordinate aspect of my argument. Yes, he says that “most” companies use open rates to stop sending emails. I don’t believe that to be true, and it doesn’t do anything to refute my argument if it is. You’ve also once again (sigh) failed to engage with any of the substance: “If users knew, they would opt-out in droves.”
> Not every HEY user is anti-tracking
Again you’d need to be a dunce to interpret this…
“I can both see [why HEY and other people hate tracking], but also would like to report to my advertisers the kind of open rate that my newsletter has.”
…as being pro-tracking. He quite literally says that the reason he wants to do it is because it’s the only way to report open rates. Sorry, but that’s not true. If you believe consumers are happy for this data to be shared with you, here are three proposals on how to do it:
1. Make tracking opt-in: on the first send to a user, include a button which says “We’d like to be able to monitor every time you open an email from us. Click here to give us permission to do it.”
Super high integrity, zero subterfuge, not a difficult thing to implement at all (even for someone with a creaky slow WordPress blog). Of course you’ll never do it because you don’t believe your own arguments — you know that consumers would barely ever click that button.
2. Make tracking a per-email thing. Include a similar button which says “Did you open this email? Click this link to let us know” and since, y’know, your users don’t mind being tracked, they’ll all happily click it, right?
3. Act with a sense of responsibility towards the world, instead of being a selfish asshole, and mandate an explicit opt-in to email tracking from your customers. So any email sent with Gmass has obtained explicit permission from its recipient to be tracked.
You’ll never do any of these things because, again, you do not believe your own arguments. You’re desperately rationalising scumbag behaviour any way you can. You’re the Trump of email surveillance: defensive, smug, incapable of keeping track of your own thoughts to the point where you openly contradict yourself, seeing mass opprobrium and feeling persecuted instead of like you have something to learn, and perhaps worst of all you have literally no self-awareness. At least Trump displays a (somewhat limited) capacity to laugh at himself.
> Well that would be like me thanking the IRS for allowing me to pay my taxes.
Believe it or not some people do think paying the IRS our taxes is a good thing, and there is simply no equivalence between the price most people gladly pay to live in a (somewhat, when you discount The Donald) functioning democratic state with social security, and what you’re doing.
> You hit the nail on the head here. If they could click their fingers and magic away it, they would do it. BUT, if they had to put 5 minutes of effort into not being tracked, they would not. Why?
Firstly: they don’t know that they’re being tracked. (That much should be obvious even to the kind of guy who thinks posing for a headshot wearing a grotesque steampunk watch makes him look cool.)
Secondly, and I can’t believe I’m having to point this out to you: many people HAVE put effort into not being tracked. You simply enable people to ignore this. It beggars belief that you can make this argument with a straight face. It’s the sort of logic I’d expect from people who injure themselves brushing their teeth.
> Because it’s likely just not that important to them. I tell myself every day that I want to lose 20 pounds. If I could click my fingers and have that happen, that would be great. But I have to put some effort into losing those 20 pounds. So then, how much do I really care about losing those 20 pounds? Probably not that much
Right up there with the dumbest things you’ve said in this thread. Nearly as good as when you compared your service clandestinely collecting and reporting information against users’ wishes to “walking through Times Square.”
> The choices or pressure? You make me sound like I’m a drug mule risking my life traveling across the border for a cartel in hopes of escaping poverty. I live a decent life, and I’m happy with most of the choices I’ve made so far.
The only thing I can think of which would position you as redeemable is to believe that you are somehow choosing to put money before a basic sense of humanity because you need to pay for your child’s medical treatment or that you spent your formative years in prison and are still developing a moral compass. As it is you seem pretty smug for someone who is having to do hilarious mental gymnastics to defend something that people hate.
> [Link to exquisitely bad take on Medium from woman with apparently zero qualifications who posts dozens of clickbait posts about how to make money from blogging]
Cool. Just so we’re clear, you’re linking to an article on Medium *advising* that nobody should give anyone advice, written by the woman who wrote an article called “How to make over $1,000 a month writing on Medium”? Not giving advice is certainly the sort of counterintuitive idea I like, although I guess we need to consider the fact that if we didn’t give advice we’d see a dramatic breakdown in civilisation on an unprecedented scale. Maybe we should pick a different messenger from a blogger? And maybe, just maybe, you should be humble and receptive to the feedback? A lot of people in this thread are calling you a scumbag. Could they be right?
> Wow. If I were a teenager, I would hashtag my response to this comment with #wowjustwow.
It comes as no surprise to me that you’re a boomer who doesn’t know that hashtags only work on Twitter.
> I care about money.
Yeah, we know.
> I care about humanity.
Except when it gets in the way of you making money.
> Which do I care about more?
Money.
> Well, if I could make all the money in the world, but all of humanity were suffering around me, I couldn’t have a lot of fun with my money, so that doesn’t work. So hmm, what if I could earn a decent living in my role as a software developer, improve the lives of my thousands of users, and not have anyone murdered by placing a tracking pixel in the emails they get? That sounds like I have money and humanity in good balance.
Except your “improve the lives of my thousands of users” happens at the cost of trampling on the privacy of everyone who uses Superhuman and HEY, and is totally avoidable. The thing you don’t seem to understand or be willing to admit is that you are going out of your way to hurt these users for money. It’s as simple as that.
> But I do believe that most people don’t MIND a company that has sent them an email knowing that they’ve opened that email.
man, Ajay, you almost said it! here, i will invert it for you, logically:
> But I do believe that SOME people DO mind a company that has sent them an email knowing that they’ve opened that email.
if you truly believe this, why not simply continue to serve tracking pixels to the vast majority of people that don’t mind (and never enable a setting or service that blocks pixels), which would allow your service to respect user choice, for free?
why spend your valuable time to explicitly screw with user choice like this?
He can’t even keep track of his own arguments. In one reply he says that he thinks people do not want to be tracked. Then he suggests that a “minority of internet users” feel violated by tracking. Then he builds something to circumvent the minority he considers to be insignificant.
It’d be funny if it wasn’t so sad. But at the end of the day his business is a tawdry little Chrome extension for scumbag marketers, so what do we expect?
I’m starting to think that if I told you that 0+0=0 AND that 0-0 ALSO equals 0, your head might explode. So at the risk of causing you an aneurysm, I’ll try explaining:
Generally, people do not want to be tracked. If you ask a random stranger, “hey, do you want to be tracked?” the answer would be “no”. It is ALSO TRUE…before I continue, let me explain what I mean by that. TWO STATEMENTS DON’T NECESSARILY HAVE TO CONFLICT. TWO STATEMENTS AROUND THE SAME CONCEPT CAN BE TRUE.
Where was I…oh, right…it is ALSO TRUE that a minority of Internet users feel violated by tracking. Let’s repeat that just for the learning:
People generally don’t want to be tracked, but only a minority of people feel violated by tracking.
> [Ignores detailed arguments elsewhere]
Cool. You seem totally open to the feedback here man. Great to see.
> Generally, people do not want to be tracked
Correct. And once again: for anyone with any integrity, this is where the conversation would stop. People don’t want to be tracked. So don’t track them. Fucking simple.
> If you ask a random stranger, “hey, do you want to be tracked?” the answer would be “no”.
Correct! Everyone hates your shitty product!
> it is ALSO TRUE that a minority of Internet users feel violated by tracking.
Except, of course, that most users do *not* know that dickweasel services like GMass track them.
If you think people don’t mind, why don’t you tell them you track them? Go on, put a message in every email and prove me wrong.
Put a big, clear message saying that you track people — and ignore their privacy settings in the process — and prove your theory. You can make all this go away.
You don’t believe it, so you won’t 😉
> A minority of internet users feel violated by tracking
Wrong. A minority of internet users know that you track them. And I can promise you that a majority of people using HEY feel violated by your specific actions to pointlessly override their privacy settings.
Hilarious watching you selectively reply to comments to avoid having to confront your own hypocrisy. No surprises to see the guy with the used car salesman profile photo behaving like one.
It’s going to take a lot to prevent myself from stooping to your level of unfounded insults, unnecessary cursing, and logical fallacies, but I’ll do my best, because I’m classy like that.
>>Correct. And once again: for anyone with any integrity, this is where the conversation would stop. People don’t want to be tracked. So don’t track them. Fucking simple.
On the other hand, my users do want tracking data. So I’m tracking. ******* simple. Why should I prioritize the desires of my non-users over the desires of my actual users?
>>Correct! Everyone hates your shitty product!
Except for the thousands of people that love my awesome product. See my reviews on the Chrome Web Store, Capterra, and G2.
>>If you think people don’t mind, why don’t you tell them you track them? Go on, put a message in every email and prove me wrong. Put a big, clear message saying that you track people — and ignore their privacy settings in the process — and prove your theory. You can make all this go away.
I would be happy to do this in my own emails that I send in my own email campaigns. I won’t make the Subject line “You’re being tracked” since that would detract from the message I actually want to communicate, but I don’t mind including it after the main message. As for doing it for every user that sends through GMass, I won’t do that, because I don’t control or even influence the content of my users’ messaging. To be clear, what you’re asking is the equivalent of:
1. Asking Google Analytics to modify their JavaScript so that a visitor to any website that uses GA sees a big banner across the top of every webpage that says “We are logging that you’re on this page and we know every other page you’ve been to, how long you were on that page, and your location.”
2. Asking every Facebook retargeting advertiser to start the text of their ad with “You’re seeing this ad because you previously visited our website X times on X, Y, and Z times”
3. Asking every mobile phone company to alert every customer before they place a phone call that “We log every number you call, what time you call, and for how long you’re on the call and will gladly hand this information over to any authority that subpoenas us for it.”
4. Asking Twitter to alert you every time you click on a t.co link with “Are you sure you meant to click this? Not only will Twitter know your IP address, location, and the URL you clicked, but in all likelihood the website you’re visiting will also know this.”
>>Hilarious watching you selectively reply to comments to avoid having to confront your own hypocrisy. No surprises to see the guy with the used car salesman profile photo behaving like one.
I’m selectively replying because 1) I don’t want to spend the time responding to everything you say, 2) A lot of what you say is childish and inappropriate, and 3) A lot of what you want me to respond to has already been addressed in either the post above or a comment in this thread. Every time you call me stupid, do you really want me to respond with “Nuh uh, I’m not stupid. You are.”?
Knic,
Your logic inversion holds true.
I understand what you’re saying — I could simply continue to serve the pixels to people that haven’t actively taken steps to block them. That’s what I was doing for the company’s entire history until I launched this new mechanism last week. I spent my valuable time, not with the intent to screw with people’s choices, but because I found it to be an intellectual challenge, which I enjoy.
After I had built it, I then decided that I wasn’t causing any harm by tracking the people that don’t want to be tracked, but I was providing a benefit to my users who want better analytics on their campaigns.
I could be wrong — perhaps I am causing harm to the people that don’t want to be tracked, and if someone can show me the harm that I’m causing, I might reverse course.
This comment represents the apex of your stupidity.
> not with the intent to screw with people’s choices
That is literally, explicitly, empirically, quantifiably, undeniably what you did. Are you fucking stupid?
> but because I found it to be an intellectual challenge
So at best your argument is that you fucked with people’s choices BECAUSE you found it to be an intellectual challenge.
From reading your description of your “solution”, your calibration on what’s challenging is roughly in line with someone who finds it intellectually challenging to punch someone in the face. What you did wasn’t hard and required After I had built it, I then [sic] decided that I wasn’t causing any harm by tracking the people that don’t want to be tracked
Utterly contemptible statement for either its stupidity, arrogance, or obliviousness. You pick which!
> I could be wrong
This comments section, and the replies you’ve received on Twitter, and your inability to justify your actions to anyone you’re engaging with, is a testament to the fact that you’re totally wrong.
> perhaps I am causing harm to the people that don’t want to be tracked
Yeah. It’s almost as if people who don’t want to be tracked have a right to not be tracked, and you’re circumventing that for no reason other than your little “intellectual” masturbation session.
> and if someone can show me the harm that I’m causing, I might reverse course.
Just to be clear, you’re not going to accept the people who’ve piled into the comments here or tweeted at you mocking you as evidence that people consider this to be harmful? What would constitute evidence?
You realise you could very easily obtain this evidence yourself by making tracking opt-in and seeing whether people do it?
Or are you saying that you want to determine what is harmful to other people? You want to control what I think of as harmful? Because that’s pretty dumb, too.
It’s hard to imagine anyone sane reading this much hate from people and thinking “I’m sooooo misunderstood”. Pitiful really.
>>It’s hard to imagine anyone sane reading this much hate from people…
I think you’re confusing your own multiple comments for multiple individual people. Ruh roh, dissociative identity disorder rearing its ugly head again?
Perfect Ajay!
That’s the thing we all expect from you. Email and Email Platforms as a whole need so many new innovations, because email is getting pushed back and back. These new innovations and new ideas will help get the email stand up and back to its original form. Keep it up! we are with you!
Thanks Mubariz!
Absolutely amazing… how an incredibly big piece of shit you are.
…says the anonymous person. Actually I’m not sure who you’re referring to, so I’ll assume George.
Wow… this thread comments is getting out of hand.
Take it easy guys !
My two cents: tracking allows personnalization, personalization allows for better customer experience, better customer experience allows for more sales with less mass market.
Success of amazon, google etc.
RGPD rules are horrible, thousands of popups with ununderstandable choices.
Gmass is a great software – we use it for our mailing monthly.
Allows” personalization”, “better customer experience”, You cannot see beyond your own personal cesspit.
Ajay Goel is a spamming douche
Spam enabling scumbag.
You folk are bastards.
You should wake up everyday and feel ashamed of yourselves for wasting your precious time in such a big dump.
Tracking functionality has stopped working since new tracking method has been turned on
My email have on the preheader text something like https://mydomain.us20.list-manage.com/track/click… I use mailchimp. What should I do to avoid that ?
Hi Freddy,
You would need to contact Mailchimp for your concern.
Wow.. these comments made me laugh a bit. Thanks for that. I was not expecting this when I stumbled on this post due to R&D. People don’t like tracking tech but honestly I think it’s here to stay. I’ve always said it’s your own responsibility to avoid tracking/have any privacy.
Lets point out.. if you use a service like gmail.. you gave up any idea of privacy a long time ago because you chose to use a “Free” service that makes money off of you. So do all the other “free” things on the internet. They exist to monetize the users activity to pay for the service it offers. Websites sell ads.. ESP’s read your email and show you ads. Martech is just more of the same to help monetize activities that may bring about a sale/transaction of some sort.
I feel Email tracking is starting to brew to the top of mind of more and more people. They are not very happy with all this data that can be known about them. They don’t want people contacting them just because they read an email. I get it. The flip side is sometimes it’s very helpful. If your in a hurry to get something done.. and this tech can speed up delivery/completion of that task, your going to like it. What most people are not happy with is this is mostly used to help speed up the “sale.” The seller wants to know who’s ready to buy and make sure to reach them fast and complete the sale before it maybe slips out of mind and for impulse purchases that’s bad. Even for very targeted sales it’s better to get it closed and moved on to the next one if at all possible. Maximizing the sales pipeline speaks this sort of jargon.
Tech to track email isn’t going away. But I do think the tools to block/stop are getting more sophisticated. I myself think there are steps that can be taken that are untraceable/undetectable without insider info getting into the public. The Author took steps I myself had assumed were methods I would use if I was trying to do the tracking.
I think tracking can be slowed down but not stopped. Again, rather than getting nasty with the author that he found a way to get around the track. And it was a very good read. Understand if you don’t like it.. work on defeating his tech.. Not calling him names. Nor is it good to be mad that you now have to work harder to be un-tracked. Truth is.. that’s never going to be easier. Don’t blame this guy… he’s just doing his job and doing it well.
You are tracking peoples online actions without their permission. You are criminal scum
If you believe that people ‘”don’t mind” being tracked, why create a work around to track people who have explicitly tried to turn off tracking?
I understand you are prioritizing your user’s interests. But your user’s interests are to undermine the explicit non consent of the public. Therefore your are undermining the explicit non consent of the public and justifying it by saying “most people don’t mind [being tracked]”. You are targeting exactly the people who have stated “I don’t want to be tracked.”
Not cool bro.
Great article, and some interesting techniques. Since I have a mailing system site that sends out emails (opted-in) for book authors, I provide ‘open tracking’ so that authors can see how many people read their emails. (Again, these are not ‘spammed’, but people who have signed up – via a double-opt-in – to receive these emails.)
I just use a server-side process that tracks the open/read of the email, via a unique ‘img src’. Currently, it uses query parameters on the IMG SRC, but that is being changed to a variable-length IMG SRC file. Some geeky stuff happens with the HTTP request for that IMG SRC which allows me to ‘count’ that request as an ‘open’.
That said, the only thing that my open tracker does is just count the ‘open’ (read). No other tracking (geocode, etc) is enabled, so that the open tracking is anonymized, and contains no private info, thereby following GDPR requirement.
Your technique game me some ideas on how to improve the process. But I think that there is a minority of people that will have the open-tracking blocked. On large lists, that amount of non-tracking might be a minor percentage of the total mailing, so not a big deal.
Hey Ajay! Found your blog when looking around for ways to disable pixel tracking in gmail.
Just wanted to say fuck you for having such an obviously shitty set of principles driving what you do, and for being deliberately obtuse about that being the case. Not gonna say anything else beyond what other people already have because it’s clear you’re just gonna willfully refuse to hear it.
Don’t bother responding because it’s clear you’re doing it under the pretense of having a reasonable discussion while not actually being open to changing your mind at all, and anyway, I’m never gonna come look at your shitty site again.
Go play in some traffic!
Wow. I came here researching background info into the art of tracking and found a great cross section of user experiences and sentiments. If I send an physical envelope recorded delivery the mailman records the status of the delivery accepted/refused/not delivered whatever. The recipient isn’t shown the contents before responding, but they can guess what’s inside before choosing to accept.
I think ethics it’s all about informed consent. And getting that consent. If this field gets any more controlled it could go down the same path that caused click bait to evolve into what it is now.
I doubt you can beat the Classic browser. Once your test-website loads press [F11].
All tracking pixels should get listed with option to add offending domains to the Hosts file, if not already there.
Have fun.
Hi Ajay,
Amazing job. Not only with the pixel stuff but with sharing with the community.
I highly appreciate your contribution and I am really impressed with your work, especially the fact that it only tracks the open when the recipient opens it. I am really curious how did you manage the opens to not track from your sent folder.
It’s ok if you want to keep it a secret 🙂
They have a chrome extension. They use it to not count the request made by the browser it is installed in. I think if you opened it on the phone app, it will still count as a read.
I believe actions are a better marker of ones value than what they say.
People say they don’t want to be tracked, but bug their own home with ‘Smart’ Speaker systems that are constantly listening to everything you say in your home.
39.3 million smart speakers sold in Q3 2021 worldwide.
Amazon alone sold 65 million Echo devices in 2021 alone.
The the next time Someone said a blog, I am hoping so it doesnt disappoint me up to this blog. What i’m saying is, Yes, it was my option to read, but I really thought youd have something intriguing to state. All I hear can be a few whining about something that you could fix if you ever werent too busy searching for attention.
I’m impressed, I have to admit. Truly rarely should i encounter a blog that’s both educative and entertaining, and let me tell you, you might have hit the nail around the head. Your notion is outstanding; the thing is an issue that there are not enough consumers are speaking intelligently about. I am very happy i found this in my look for something in regards to this.
excellent issues altogether, you simply received brand new reader. What could you recommend about your put up that you simply made a few days in the past? Any sure?
When I originally commented I clicked the -Notify me when new surveys are added- checkbox and after this every time a comment is added I recieve four emails using the same comment. Could there be in whatever way you may eliminate me from that service? Thanks!
An intriguing discussion may be worth comment. I’m sure you should write much more about this topic, may well be described as a taboo subject but generally folks are too little to chat on such topics. An additional. Cheers
Hello, Neat post. There is an issue along with your website in internet explorer, might test this¡K IE nonetheless is the marketplace chief and a big section of people will pass over your excellent writing due to this problem.
enoyed the read, well i didnt cause i didnt agree but well explained.
Aw, this became an extremely good post. In notion I have to put in writing like that moreover – taking time and actual effort to produce a really good article… but exactly what can I say… I procrastinate alot and no indicates manage to go carried out.
I appreciate the new perspective you provided to the subject.
There are definitely a whole lot of details like that to take into consideration. That could be a nice level to deliver up. I supply the thoughts above as normal inspiration however clearly there are questions just like the one you bring up the place crucial thing shall be working in honest good faith. I don?t know if greatest practices have emerged around issues like that, but I’m sure that your job is clearly recognized as a good game. Each girls and boys really feel the affect of just a moment’s pleasure, for the rest of their lives.
There is noticeably big money to learn about this. I assume you have made certain nice points in functions also.
There is noticeably a bundle to know about this. I assume you made certain nice points in features also